Introduction
The challenges in countering drones are faced in both war and peacetime. As discussed in the previous chapters of this book, the risks presented by drones have increasingly come into the civilian focus over recent years. In particular, the incidents at Gatwick Airport (cf. Chapter 3, p. 48) and their consequences for flight safety, flight operations and, above all, economic losses have clearly illustrated this.1 However, drones do not only threaten large facilities such as airports or military installations. The range of critical civil infrastructure is immense and in contrast to burglary and fire protection, awareness of the potential threat posed by drones is far from being widespread. Therefore, this chapter is intended to show which areas of critical civil infrastructure are exposed to a possible threat from drones, what these threats may consist of, and how they can be dealt with pre-emptively because civilian businesses usually do not possess the legal authority to employ most of the active counter-measures discussed in this book.
Critical Civilian Infrastructure
Depending on the country, the definition of what constitutes critical infrastructure varies slightly. The German Federal Office for Information Security defines critical infrastructure as ‘organizational and physical structures and facilities of such vital importance to a nation’s society and economy that their failure or degradation would result in sustained supply shortages, significant disruption of public safety and security, or other dramatic consequences’.2
The United States’ Cybersecurity & Infrastructure Security Agency defines 16 critical infrastructure sectors (cf. Figure 17.1) ‘whose assets, systems, and networks, whether physical or virtual, are considered so vital […] that their incapacitation or destruction would have a debilitating effect on security, national economic security, national public health or safety, or any combination thereof’.3
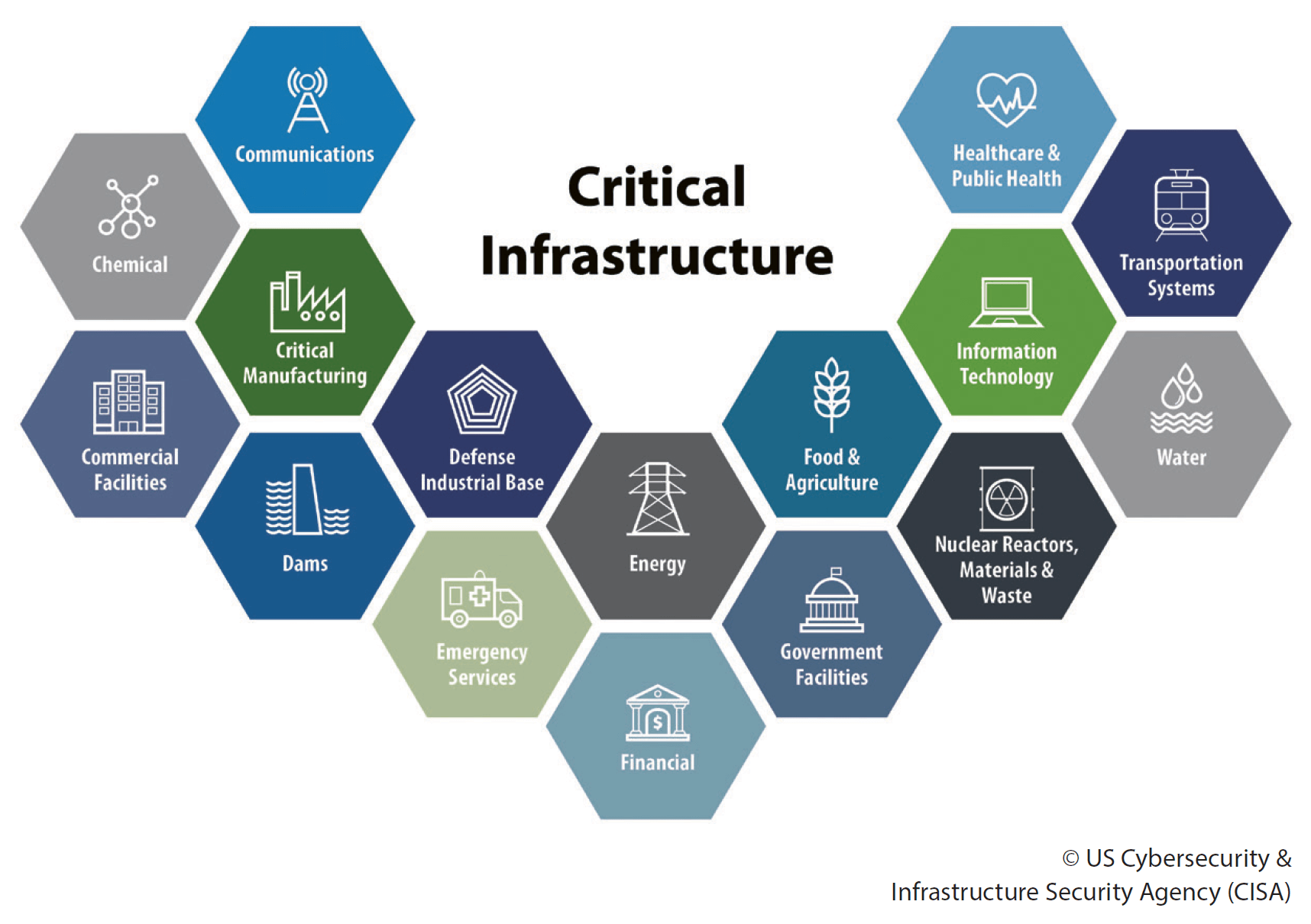
Critical infrastructure components are, to a large extent, dependant on one another. Agriculture requires the supply of clean water, water purification and pumps require electricity, and electricity may be generated from the stored water behind a dam. Interference with transportation systems may cut off supplies for critical manufacturing and medical services. Communications, information technology and financial, commercial as well as public services are closely interlinked. These are just a few examples of how the disruption of a single critical infrastructure can trigger a series of effects that, together, can have far worse consequences.
Therefore, any critical infrastructure has usually an emergency response plan in place to cope with any threats that may interfere with its operation. With the increasing proliferation of drones, a new threat has emerged that now requires consideration and incorporation into these response plans.
The Drone Threat – New Wine in Old Skins?
Critical infrastructure – civilian as well as military – has always been protected against the threats of its time. For centuries, even the principal threats have not changed, including burglary, theft, espionage and catastrophic damage to property and lives. Since the Great Wall of China, the construction of walls and fences around a site has been and still is the standard measure to protect it against the aforementioned threats. The computer age was the first real game-changer by offering a new attack surface for an adversary, namely the internet and its connected networks. But even in this new cyber domain, the traditional threats remain unchanged and the standard measure is – again – building a digital variant of a wall, commonly known today as a ‘firewall’. The ‘drone age’ is not different. It just offers a new attack surface, the air domain, for the same set of threats, whereas the air domain is not even new, but it’s now accessible for the broader public.
The 2019 Global Cyber Risk Perception Survey conducted by Marsh and Microsoft revealed that cyber-attacks are the predominant concern of international businesses, outranking other threats like criminal activities, industrial accidents, espionage or terrorism by a wide margin.4 Because drones were not even part of the questionnaire it could be concluded that the current perception of their threat is rather low. However, it could also be argued that drones themselves do not represent a new type of threat, but could rather be seen as a new means of delivery only. Therefore, the following sections briefly outline how the initially mentioned centuries-old threats can be delivered by a drone and where traditional countermeasures continue to be sufficient or are being challenged.
Burglary
Burglary is typically defined as the unlawful entry into a structure with the intent to commit any crime inside. Traditional protective measures include, but are not limited to, building walls and fences around the structure, closing and locking gates, doors and windows, or employing a guard force. These measures either try to physically prevent access to the building or deter illegal activities by threatening the offender with detection, identification and prosecution.
Drones offer an offender the possibility to bypass any physical barrier by simply flying over them. Current consumer models reach altitudes of several hundred metres with ease. If no dedicated drone detection system is in place, chances are high, that this intrusion will even go undetected if properly planned. For example, guard shift changes or visual conditions at dawn, dusk and night may open a window of opportunity for an intrusion attempt. Drones also offer the advantage of minimizing the offender’s risk of being identified and prosecuted, even if the drone is captured.
In peacetime, it is extremely challenging to prevent the intrusion of a drone as legal restrictions prohibit the use of active defence systems in many cases. It is therefore important to realize that burglary usually has a purpose, which is to commit one of the crimes described below. So even if it cannot deny access to the property, a reliable drone detection system will help to take the appropriate security response and measures to prevent the drone from fulfilling its mission.
Theft and Industrial Espionage
The term theft is used widely to refer to crimes involving the taking of a person’s property without their permission. In our information age with businesses operating globally, not only physical, but also to a greater extent intellectual property has large monetary value. Physical property is typically secured by the measures of the structure hosting it. Sometimes it is additionally protected to either prevent unauthorized access to the property or to prevent removal of the property itself. In the cyber domain, this concept is represented by firewalls preventing access or by encryption of the property to prevent theft and espionage.i
Apart from specialized bomb disposal robots, drones are not (yet) designed to remove physical property from a structure. However, this is different with intellectual property. Current consumer drone models are typically equipped with electro-optical high-resolution cameras which are often also capable of sensing in the infrared spectrum. Drones may also be reconfigured with highly sensitive microphones to capture voice communications or even with a high-power wireless network repeater to force wirelessly networked devices and mobile phones to connect to the drone and, in turn, capture their communications.
Long established security measures for the protection of intellectual property and sensitive information can significantly hinder a drone from accomplishing its theft or espionage mission. It just has to be recognized that height no longer provides protection and every window, no matter on which floor, is prone to a drone’s high-resolution camera and microphones. Closing the window and its curtains easily prevent a drone from taking any imagery. Arranging the office so that no sensitive information faces a window is also an option. Classified meetings can be held in windowless rooms so that no sound can be sensed through any windows or outside walls. Strict enforcement of cybersecurity measures not only for the company’s computer systems, but also for the personnel and the private hardware they bring with them, would help reduce the risk of a drone-based cyber-attack.
Damage to Property and Life
Threats which may cause fatal damage to property and human life can range from unintentional, unwitting, or careless actions by one’s own staff, resulting in an accident, up to intentional, willful, or malicious acts of crime or terrorism.
Accident prevention is an integral part of even a small business’ operations and is usually required by law. New structures are usually planned with fire protection and extinguishing systems right from the start. Fire drills are often mandatory to be performed at least once a year. Evacuation plans or information on hazardous substances are typically displayed prominently for everyone to see. All these measures contribute to raising the awareness of existing threats and to educate the staff on the appropriate mitigation strategies. Expanding on this principle by displaying information about drones and educating personnel on a corresponding mitigation strategy would help them to better respond to a potential drone incident.
Run a drill. You don’t have to have a flying object to run drill any more than you have to have a fire to have a fire drill.
Richard Lusk, Director, UAS Research Center, Oak Ridge National Laboratory
Defending against criminal or terrorist acts in the civilian domain is usually limited to passive protection measures, as businesses do not possess any (or very restricted) legal authority to employ potentially lethal force against an intruder. Apart from the external protection of the premises, additional access controls, baggage screenings or metal detectors are often used to prevent the introduction of weapons and other dangerous materials into the structure. Drones can be used to bypass these security measures and to deliver hazardous materials into the site, near the outer walls or on rooftops of a structure, where these materials may range the entire Chemical, Biological, Radiological and Nuclear (CBRN) spectrum. Similar to the aforementioned accident prevention measures, establishing shelters or evacuation points and maintaining the respective drills can help to mitigate the effects from criminal and terrorist acts.
Indications and Warnings
Not every drone sighting is an attempt to compromise the site and spy on the business’ intellectual property. Not every drone sighting is an attack. Indeed, it can be assumed that most incidents are caused by drone operators who either act carelessly or simply unknowingly violate the boundaries of a property. Drone detection systems can help to establish patterns of routine drone presence in the area and detect unusual flight activity that may indicate a potential threat.6 Moreover, law enforcement, intelligence, and other related agencies need to provide appropriate indications and warnings to help businesses build and maintain a sufficient level of situational awareness so they can adjust their mitigation strategies against potential criminal or terrorist threats accordingly.
Threat Analysis and Risk Assessment
Threat Analysis and Risk Assessment are two sides of the same coin. To recognize potential drone threats, they first need to be distinguished from the regular and lawful airspace users. Once recognized, the drone model and its capabilities need to be identified to further proceed with a risk assessment, i.e. the evaluation of the drone’s potential actions that could negatively impact the critical infrastructure’s ability to operate. Without proper data put into the risk assessment, an organization is likely to remain vulnerable to their top priority threats without even knowing of their existence.
Therefore, airspace activity data must first be collected and thoroughly analyzed. Airspace activity data is gathered through detection hardware, such as radio-frequency sensors, cameras, microphones, or radar. These sensor inputs are then fed into a software program, which can process the raw data and provide a situational picture over time and statistics of the respective airspace for further analysis. Emphasis is placed especially on the following statistical information:
- On average, how many drones are regularly operating in the respective airspace?
- On which days, at what time, and how long are specific numbers of drones operated in the respective airspace?
- What kinds of drones are being used?
This data helps to build a statistical drone usage profile for a critical infrastructure’s airspace and its surroundings, which, in turn, helps to identify deviations from the statistical norm. These deviations are the first indicator of a potential threat. Hence, the information-gathering process is the most important, but at the same time, the most challenging step for critical infrastructure security leaders to begin. Building a statistical drone usage profile can take several months until sufficiently meaningful data is collected.
Once a solid statistical picture is available, security teams can start analysing questions, such as:
- Can drone activity be correlated with standard operational activities within the organization such as shift changes or shipping and receiving?
- Does the level of attention from outside organizations such as competitors or media change the level of drone activity?
- Are drones appearing during special events outside of normal operations, whether they be quarterly forecast meetings, prior or during major acquisitions or announcements, or arrive when special guests are on-site?
- What are the flight patterns of the drones? Do they reveal common flightpaths or areas on the property which may require additional security?
With these insights, backed by statistical data and a solid drone usage profile, security personnel can adequately detect deviations from regular air traffic and identify potentially malicious intent of non-compliant drones.
Planning and Integrating the Countermeasures
Not every drone incident requires security teams to actively interfere with the drone or even to take it down. Simple passive measures to counter a potential threat have already been described in the previous sections. But it is important to have a drone mitigation plan prepared and exercised. It should be the norm that a drone mitigation plan is mandatory for any critical infrastructure, very much like it is required to install fire extinguishers, first aid kits, and emergency exit signs, as well as having personnel trained in emergency response or the company’s data security policy.
The following passive techniques and measures may be considered when developing a drone mitigation plan.
- Sirens, loudspeaker announcements, flashing lights: The most actionable of all countermeasures. This strategy not only ensures that the drone pilot knows he/she has been spotted, but it also can trigger other ground support to implement further emergency or protective procedures.
- Leading people and sensitive materials to safety: The first action should be to minimize the risk of injury to people and/or the destruction of property, whether it be to move an outdoor gathering away from a hovering drone, or cover and hide sensitive property or prototypes from view.
- Dispatching security teams to locate and apprehend the drone pilot: Modern drone detection systems can not only detect a drone in mid-air, but also triangulate the location of the remote control. Security teams can use this information to get hold of the operator and hand him/her over to law enforcement authorities. The statistical drone usage profile also helps discover patterns in drone activity which highlights airspace vulnerabilities, and allows security to strategically target areas with the most drone activity.
- Integration of IoTii capabilities for automated responses: Especially when protecting intellectual property or large groups of people, drone detection systems can be integrated into additional security technologies, such as automatically or manually deploying retractable roofs, lowering window blinds, closing doors or enabling additional physical security measures.
There are many ways that location information can be used to either locate or deter operators who are flying their drones where they shouldn’t. It is well worth considering the variety of passive responses that are now possible via the integration of real-time detection data. Although it is only natural to think of defeating unwanted drones, that option is not available to most organizations.
However, when passive mitigation measures are not enough, and the last option is taking down unwanted drones it is essential to layout what technologies and assets are available, as many defeat systems are restricted or reserved for governmental use only. All organizations can implement defensive responses to drone incursions, but explicit legal authorities must be granted for those using offensive techniques.
As is the case with deploying a suitable detection solution, there are several factors to consider when using offensive techniques, including:
- Physical environment: The physical environment where mitigation is desired is the first major driver and challenge to determine mitigation options. A vast physical space, such as an airport or military installation poses entirely different challenges from a building or campus in a dense, urban environment.
- Legal authorization for use: Laws vary across countries for different organizations on how they can defeat drones. The US federal government specifically prohibits the interference with a drone’s operation with very few exceptions. To implement offensive mitigation techniques, users need to research and understand what the legal prohibitions are and what organizations and situations are exempt from compliance.
- Current policies and security procedures: Some organizations already have existing policies and procedures that define how security teams will respond to reports of drone sightings. In many cases, visual identification of an incursion is first required for further reporting and action, which is often too late with regard to a drone flying on average between 10 and 15 metres per second at full speed.iii
Offensive mitigation techniques include kinetic and non-kinetic solutions that will either ‘hard-kill’ (destroy the drone hardware) or ‘soft-kill’ (interfere with the drone software or operating system). Kinetic solutions involve some form of physical motion that interacts with the drone hardware, for example.
- Hard-Kill: Shotguns, bullets or other projectiles will destroy or damage the drone
- Soft-Kill: Net guns or net drones can be deployed to capture the drone, and keep it intact for forensics
Non-Kinetic solutions do not involve a physical motion, but rather an electronic or technological interference, for example.
- Hard-Kill: Directed-energy such as lasers and dazzlers use technology to destroy the drone’s hardware
- Soft-Kill: Jamming and protocol manipulation may force the drone to land, return to home or enable another pilot to commandeer the drone and control the flight path
It is still reasonable to deploy defensive strategies first, and then escalate as needed and authorized with offensive tactics to protect assets. It should be noted that many if not all of the offensive measures are usually reserved for the law enforcement authorities. Therefore, close cooperation with the police and incorporating them into the drone incident response is often required to successfully implement an adequate drone mitigation plan.
Summary
Drones are a new tool to deliver century-old threats. Hence, it is not always necessary to develop new mitigation strategies. There are a variety of established measures which are more than adequate to counter a drone threat and which can easily be adapted and implemented into existing emergency response plans.
However, drone threats are not yet commonly recognized, and many critical infrastructures lack a drone mitigation plan. Gathering drone traffic data is a prerequisite for developing a statistical drone traffic profile which enables businesses to understand the actual scope of the threat. It should be a matter of course to have a drone mitigation plan in place, just as there is a plan for fire protection. Obviously, this also needs to be exercised in regular ‘Drone Drills’.
Finally, active measures are almost always reserved for law enforcement agencies. Hence, close cooperation with the police is required to establish an adequate drone mitigation plan which can hold against even a worst-case scenario.